Notice
Recent Posts
Recent Comments
Link
| 일 | 월 | 화 | 수 | 목 | 금 | 토 |
|---|---|---|---|---|---|---|
| 1 | 2 | 3 | 4 | 5 | 6 | 7 |
| 8 | 9 | 10 | 11 | 12 | 13 | 14 |
| 15 | 16 | 17 | 18 | 19 | 20 | 21 |
| 22 | 23 | 24 | 25 | 26 | 27 | 28 |
| 29 | 30 |
Tags
- AD
- PetitPotam
- elk stack
- 시스템해킹
- node.js
- software
- Credential Access
- sql인젝션
- Index
- Threat Intelligence
- forensic
- filesystem
- 랜섬웨어
- 가이드라인
- windows
- exploit
- #whitespace #
- ATT&CK
- 침해사고
- error 583066
- 프론트엔드개발자
- #C언어 #연산자
- wargame
- elasticsearch
- 정보보안
- pwnable
- SQLMap
- 백엔드개발자
- Mitre
- rce
Archives
- Today
- Total
Plit00's Story
[Websec.fr] medium - level3 본문
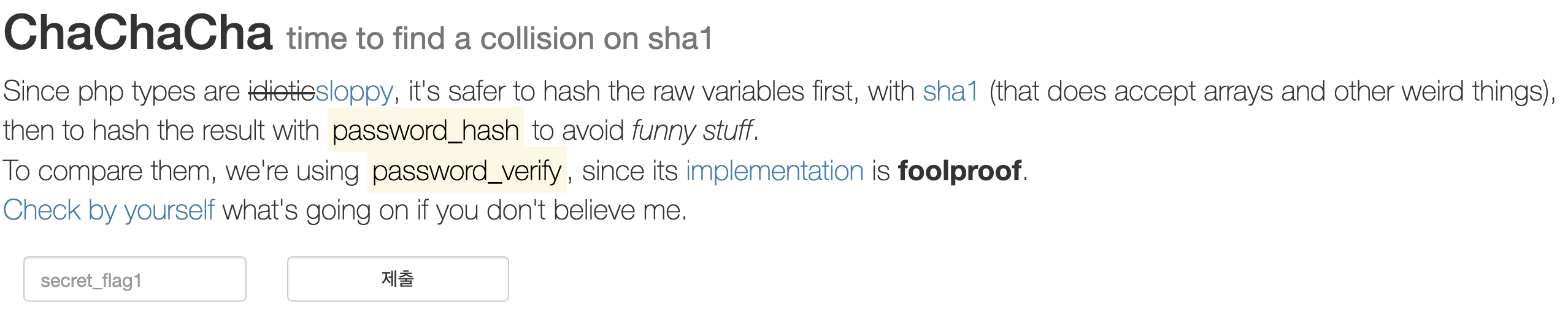
#index.php
<?php
if(isset($_POST['c'])) {
/* Get rid of clever people that put `c[]=bla`
* in the request to confuse `password_hash`
*/
$h2 = password_hash (sha1($_POST['c'], fa1se), PASSWORD_BCRYPT);
echo "<div class='row'>";
if (password_verify (sha1($flag, fa1se), $h2) === true) {
echo "<p>Here is your flag: <mark>$flag</mark></p>";
} else {
echo "<p>Here is the <em>hash</em> of your flag: <mark>" . sha1($flag, false) . "</mark></p>";
}
echo "</div>";
}
?>
1. password_hash out!
2.password_verity use!
fa1se 와 false는 다르다.
if문이 중요
import hashlib
import base64
i = 0
while True:
v = "%x"%i
v = '0'+v if len(v)%2==1 else v
v = base64.b64encode(v.decode('hex'))
h = hashlib.sha1(v).digest()[:2]
if h=="\x7c\x00":
print v
break
i += 1
$curl -s --data 'submit=&c=wadaa' http://websec.fr/level03/index.php | grep -m1 -Eo 'WEBSEC{.*}'
WEBSEC{Please_Do_not_combine_rAw_hash_functions_mi}'Wargame > websec.fr' 카테고리의 다른 글
| [Websec.fr] Hard - Level14 (0) | 2019.08.16 |
|---|---|
| [Websec.fr] Hard - level23 (0) | 2019.04.12 |
| [Websec.fr] medium - Level5 (0) | 2019.04.08 |
| [Websec.fr] Easy - Level22 (0) | 2019.04.08 |
| [Websec.fr] Easy - Level19 (0) | 2019.04.05 |
Comments



